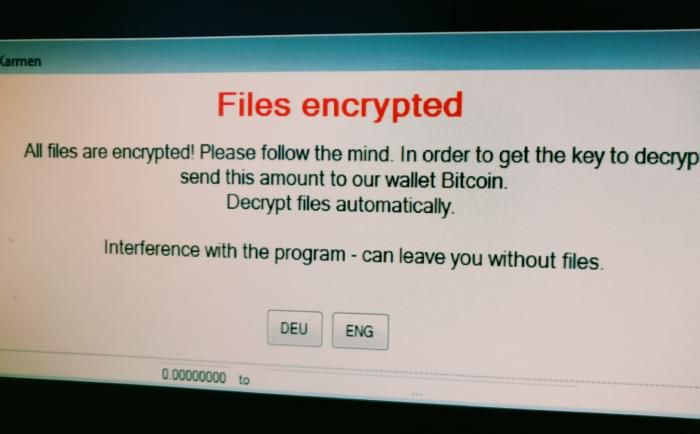
What’s new in ransomware?
In June, South Korean hosting company Internet Nayana, Inc., was hit by a ransomware attack that took down its 153 Linux web servers -- home to more than 5,000 customer websites. "I know that negotiations with hackers should not be done," company CEO Hwang Chilghong said in a statement. "I would not negotiate with a hacker if it was the case that it ended in the damage of my own company alone. However, the scale of the damage was too great and too many people would suffer."
The company wound up paying nearly 400 Bitcoin to get its data back, which at the time was more than US $1 million. That was just part of the total costs the company incurred. In addition to the time and money spent on the recovery, the company had to give discounts and refunds to affected customers. Not all data could be restored, and the company promised affected customers free hosting for life.
Nayana isn't alone. Earlier this month, shipping giant Maersk says that a ransomware attack got into the company's systems via an automatic accounting software update. The cyber attack affected users and applications in 500 locations, the company says. While no data was lost, the recovery and loss of revenues is estimated to cost Maersk between $200 and $300 million.
And in a July earnings call, global pharmaceutical giant Merck admitted that a ransomware attack the previous month disrupted worldwide operations, including manufacturing, research and sales, and that some manufacturing operations still weren't restored.
Altogether, more than a million computers were infected by WannaCry, Kryptos Logic CEO Salim Neino told Congress earlier this summer. According to Cybersecurity Ventures, global ransomware costs will exceed $5 billion this year, up from just $325 million in 2015.
The reason? The attackers, seeing the potential for massive payouts, have been innovating furiously. The security industry has also been working hard to improve defenses, but it's hard for individual enterprises to stay up to date. As a result, the situation is likely to get worse before it gets better, experts say.
WannaCry, Petya and Shadow Brokers, oh my
Dominating this year’s headlines was the damage caused by the WannaCry and Petya ransomware attacks, and of the Shadow Brokers leak of NSA hacking tools such as the EternalBlue exploit that these two ransomware attacks used.
"There are new variants every day," says Brian Bartholomew, senior security researcher, Global Research and Analysis Team at Kaspersky Lab ZAO. "It's more than a full-time job just to keep track of all the families out there."
Ransomware attackers don't just use new malware variants. They are also launching attacks that require no software downloads at all. Instead, the attackers take advantage of the tools and software that already exist on the victim's machine, or that just run in memory.
"So traditional anti-malware approaches are useless," says Dan Schiappa, SVP and general manager of Sophos end user and network security groups at Sophos Ltd. "The ball just moves to another game," he says. "We raise our defenses and the bad guys just find another attack vector."
New attack strategies
New exploits are just the tip of the innovation iceberg when it comes to the ransomware industry. Attackers have adopted new strategies for infiltrating networks, improved their ability to do damage, and, just as important, have embraced sophisticated growth-enabling business models.
For example, users have been getting training on not clicking on malicious attachments or visiting malicious sites, and anti-malware vendors have been getting better at spotting those sites and attachments. But worms spread themselves without the user needing to do anything at all. "The worm will look and scan its surroundings on the network that have the vulnerability that it is looking to exploit, and copies itself onto the exploited machines," says Robert Simmons, director of research innovation at ThreatConnect, Inc., a security vendor based in Arlington, Va.
A company that has a vulnerable machine connected to the internet is an easy target, for example. If a company has locked-down all its public-facing computers, an employee might use a mobile device or laptop to connect to an insecure network that has another infected machine on it, Simmons says.
Then, once the employee is back on the company network, the ransomware can spread from there. Once inside, the attackers don’t only launch encryption right away, he adds.
"With Petya, they found that in addition to its ransomware capabilities, it had a tool to provide an additional capability of attacking Windows domain controllers, the locations where the credentials and passwords to your network were kept," he says. "So they're branching into other capabilities that would let them pivot around the network."
The attackers can steal data, for example, or do other damage. Then the ransomware will go off, and help the attackers cover their tracks. "The ransomware would be used as a smokescreen," he says. "It would make it more difficult for a responder to find evidence of the original attack."
What about backups?
If ransomware gets through and encrypts everything, a company can still wipe the infected machines and restore from the most recent good backup, right? Not necessarily.
It's become common for ransomware to stop the Windows Shadow Copy service and delete all the backups already created, says Nikolay Grebennikov, VP of research and development at Acronis, a data backup vendor. In fact, in tests by AV-Test and Anti-Malware Test Lab conducted earlier this year, most popular personal backup software failed to protect the backup files from ransomware.
Even enterprise-grade backup platforms can fall victim, such as Veeam, a backup and recovery vendor that claims more than a quarter-million business customers. Earlier this spring, a customer reported that attackers gained access to credentials and erased the backups.
Other techniques that ransomware writers use include getting digital signatures for their malicious code, so that it doesn't register as a threat, says Acronis' Gerbennikov. His company was the only one to score well in both the AV-Test and Anti-Malware Test Lab reports. "Backup vendors never thought about this, and have almost zero self-protection," he says. "But self-protection is a crucial component of protection right now."
Once someone in the ransomware community comes up with a new attack method, it spreads quickly. Inventors sell their tools, or license them to distributors. "They have these kits that you can buy to create your own ransomware attacks," says Kaspersky's Bartholomew. "Just target the people you want, and off you go. Now they also have ransomware as a service. It's becoming more and more readily available and easy to use."
Heuristics, AI, and other next-gen protections
Traditional signature-based antivirus can't keep up with new variants, new zero-days and infections that don't depend on executable files. As a result, traditional antivirus vendors and new endpoint protection vendors have both been offering next-generation protection capabilities such as sandboxing and behavioral analysis.
Even free and low-cost antivirus products are adding advanced detection tools to their signature-based approaches. "The free version of our antivirus comes with all the normal detections that you would have in a paid version," says Bartholomew. "That includes behavior and heuristics. Most of the large antivirus companies have some level of heuristic detection in their engines."
McAfee, for example, is taking a multi-layered approach. "The first layer is [traditional] signature-based antivirus," says Raja Patel, VP for corporate product at McAfee LLC. "The second layer is watching for behaviors." Say, for example, something is trying to encrypt a lot of files, or the entire C drive. "That seems a little iffy, you don't want to allow it to do that," he says.
Companies can stop that behavior, or send it to a containment environment where they can take a look at it, Patel says. "And the third layer is machine learning. You can start trying to separate what is malicious from that is not malicious."
In addition to the traditional vendors, a new crop of security vendors are on the market specifically focused on next-generation malware detection that is designed to either replace or supplement traditional signature-based antivirus. They were out in full force at Black Hat this summer.
Sean Pike, an analyst at International Data Corp., says that nearly every endpoint protection vendor he talked to at the Black Hat conference this summer reported zero ransomware infections. "A lot of the vendors are messaging that they've solved ransomware," he says. "Which leads you to wonder where all these newsworthy infections are coming from." It's not that the ransomware is still getting through the protections, he says. It's that the machines weren't protected in the first place.
"There's a tremendous amount of inertia built into the process of upgrading and updating and getting to the absolute latest and greatest," says Rod Murchison, VP of product management at CrowdStrike, Inc., which offers cloud-based next-generation endpoint protection. "It's like going from Windows 7 to Windows 10," he says. "If it takes you six months to get new software deployed, you're always going to be behind on your zero-day protections."
Some of the most damaging attacks recently have involved known exploits for which patches were available. Enterprises may delay updates to avoid network congestion, in order to perform their own testing, or because they're running legacy systems that can't be updated. "We still find companies that haven't patched systems in months, or even longer," Murchison says.
What's next?
An individual hit by a ransomware attack can be expected to pay up to a few hundred dollars to clear up an infection. The ransom amount goes up when companies are hit, with the average company paying $2,500 per attack, according to a report by Ponemon. In addition, 7 percent of companies hit by ransomware pay more than $10,000.
When a cloud provider is hit, one that services large numbers of enterprise customers, that payout can be a lot higher. The attack against Nayana could just be the start. "We really think that's the next frontier," says IDC's Pike. In a recent survey the research firm conducted, 80 percent of ransomware victims says that at least one of the ransomware attacks they saw was related to cloud infrastructure.
At the end of the day, no amount of protection is going to be enough since the bad guys will always be innovating -- and only need to be successful once. Law enforcement will also need to step up, putting cyber criminals behind bars. That requires time, however, and a lot of inter-agency cooperation since the attackers tend to be all over the world and key infrastructure is hosted in areas with the poorest enforcement. "We have only seen a couple of arrests here and there, but we know that there are some ongoing efforts in this area," Pike says.
The flow of money also needs to be addressed. "My feeling is that long term, cryptocurrency will be regulated," Pike says. "But I don't think we're anywhere near there yet."
